Recently I developed a system where the client wanted each user to only be able to see his or her own entries, and thanks to Custom Menus, some judicious scripting, and a bit of trial and error, this was accomplished.
I was feeling rather pleased with myself when the client asked, “What about the Keychain?” Well, what indeed? The Macintosh OS has a feature called the Keychain that “helpfully” offers to remember login credentials so that users don’t have to repeatedly type them in.
So imagine a situation where User A has instructed the Keychain to remember login credentials. What happens if User B gains access to User A’s computer, and opens the database? That’s what the client was wondering… actually, he knew what would happen (User B would gain access to User A’s entries). The question he was really asking was, “What are you going to do about it?”
Hmmm… well… FileMaker’s Perform AppleScript command might be able to clear out offending Keychain entries, but preliminary research indicated it would be more of a headache than I was inclined to take on.
Here’s what I decided to do instead (I call this the “path-of-least-resistance” approach).
1. Set the solution to auto-login with a low-level account and password (by “low-level”, I mean that the associated privilege set has minimal privileges).

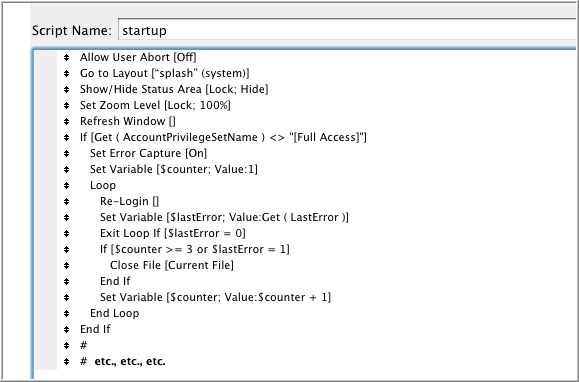
2. Configure the startup script to…
- take the user to a safe, locked-down layout
- perform the Re-Login command
Here’s a simplified version of the startup script.
The user is given three chances to log in with proper credentials… if they can’t provide them, or if they click the Cancel button, the file closes.
I decided to use Close File rather than Exit Application because while quitting FileMaker might be appropriate action for an unauthorized user, it could seriously annoy a legitimate user in the middle of working on other FileMaker files.
Now users can check the “Remember this password” box to their hearts’ content, but they will always be required to manually log in with proper credentials.


Hi Kevin,
By chance, I have implemented a very similar arrangement in one of my core solutions, albeit for different reasons. Basically, I am intending to add particular FM Go functionality but I haven’t gotten it done yet. Nevertheless, I wanted to begin the process of ‘training’ my users to be more comfortable with relogging in, and consciously selecting access privileges, depending upon the task in hand, ie ‘just sharing’ or actually doing data changes.
The one hiccup that I’ve found: importing.
If I need to import data from one file to another, I now need to remember to open the source file and relogin with sufficient privileges, prior to attempting the import.